Setup SeekTable single sign-on with MS Entra ID
To enable single sign-on on your self-hosted SeekTable installation you need to have active Single sign-on subscription. If you want to evaluate this feature before purchase you can request a free 14-day trial.
Part 1: App Registration in Microsoft Entra ID
Note: you need to have "Global administrator" role in your directory.
-
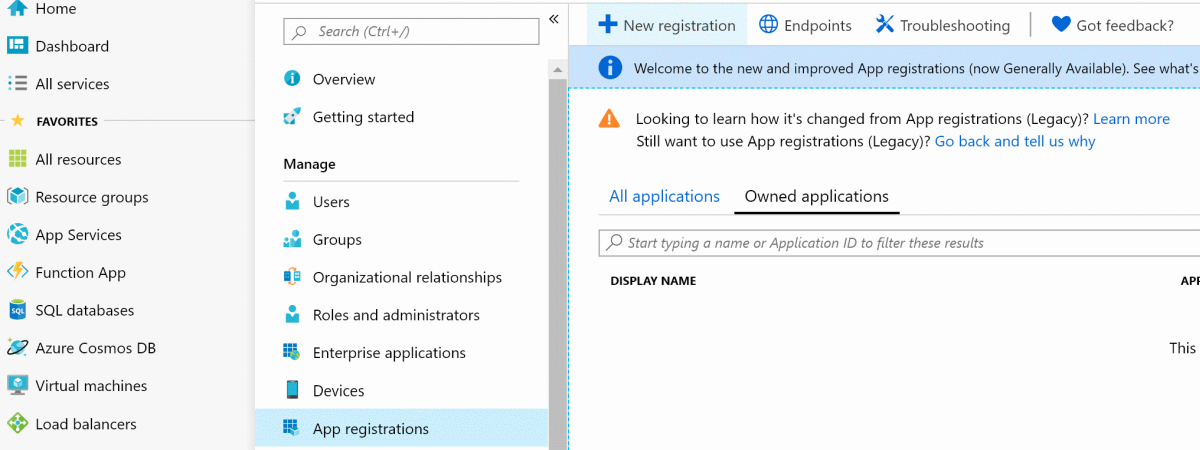
Go to entra.microsoft.com
→ Entra ID → App registrations → New Application Registration:
- Enter application name and self-hosted SeekTable URI:
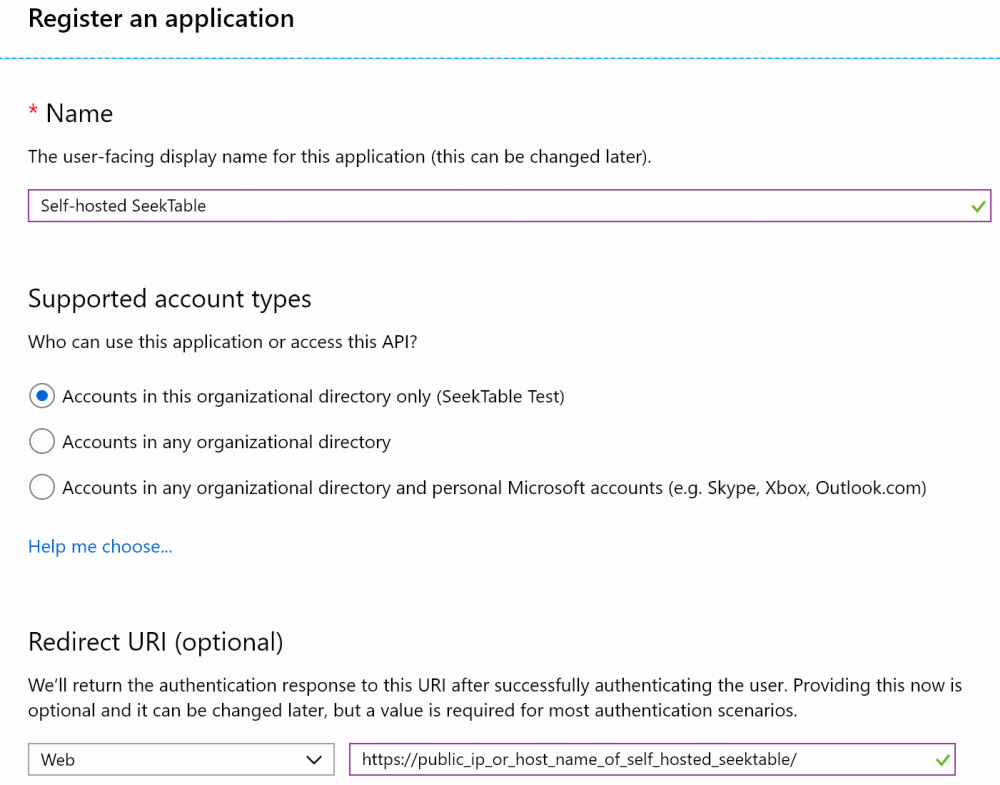
NOTE: you can usehttp://localhostfor testing purposes but for non-localhost HTTPS is required. To enable HTTPS for self-hosted SeekTable you can use NGINX as a reverse proxy and configure it to use SSL sertificate (if you don't have it you can get it for free with Let's Encrypt).
- Go to Endpoints and copy Federation Metadata Document URI:
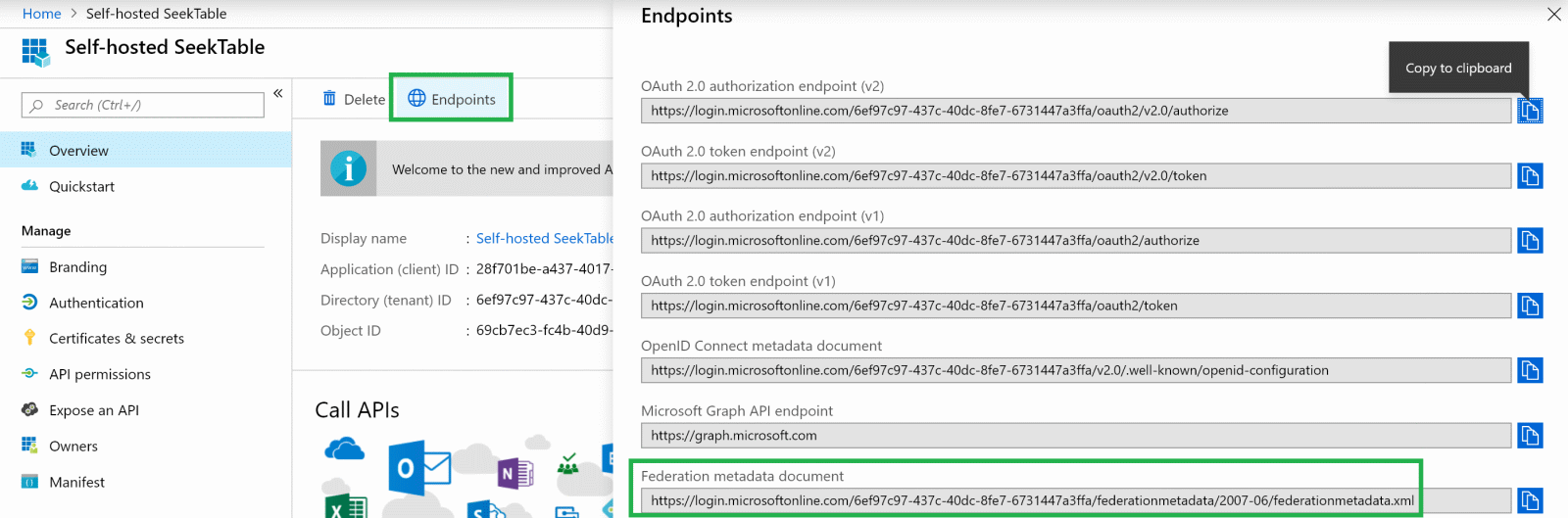
This is a value forMetadataAddressSeekTable SSO setting (described below).
- Go to Expose an API , click on Set near Application ID URI and then Save:
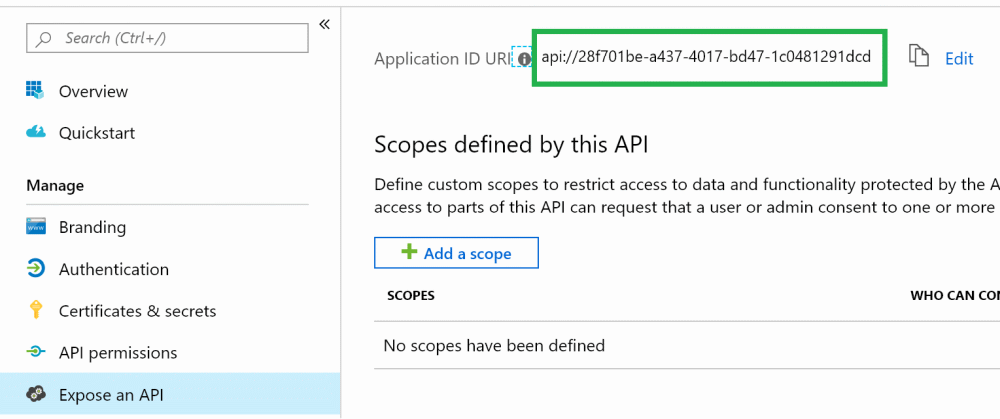
This is a value forWtrealmSeekTable SSO setting (described below).
Part 2: Configure SeekTable SSO settings
Find docker-compose.seektable.env file and add the following lines:
SeekTable_ST__SsoWsFederation__Wtrealm=Paste_Application_ID_URI_here SeekTable_ST__SsoWsFederation__MetadataAddress=Paste_Federation_Metadata_Document_URI_here SeekTable_ST__SsoWsFederation__LocalLoginDisabled=false SeekTable_ST__SsoWsFederation__LoginButtonText=Login with Entra ID
Re-create self-hosted SeekTable docker containers (docker compose up); after that a new button should be present on the Login page:
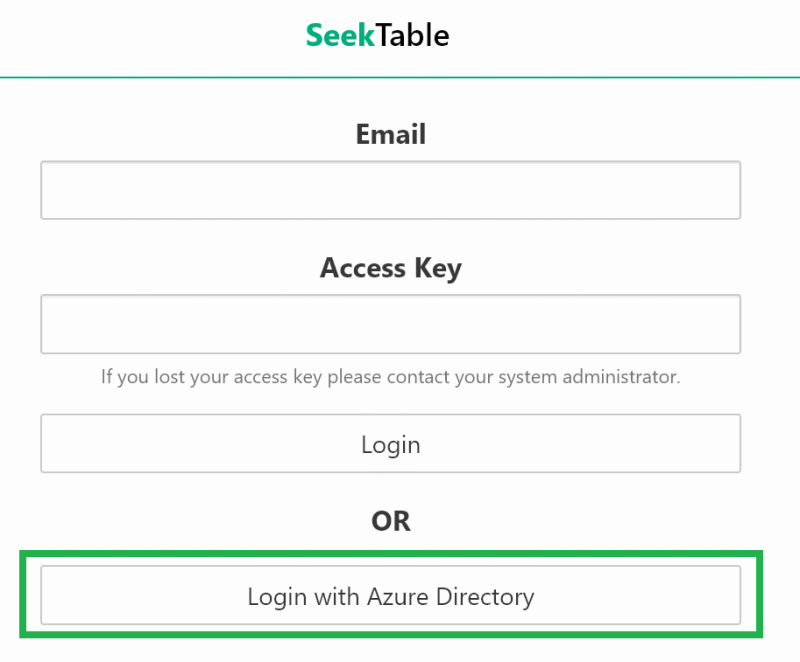
If SSO works correctly you can set LocalLoginDisabled=true to disable login form at all (only SSO with Entra ID will be allowed).